Docker 101 : Networking basics
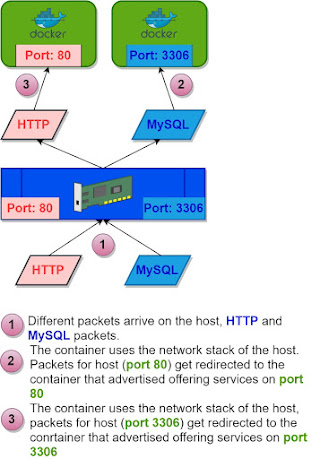
In that mode, when the process starts within a container, it will attach to a port and use to the host's network stack.
The container will be using the network (TCP/IP) stack of the host.
The diagram below illustrates that through HTTP and MySQL packets.
Remark:
In the host-based networking, we can't run two containerized services with the same service port on the same host. For example we can't run two containers running web servers both on port 80 on the same host.
Example (containerized services on different ports on the same host):
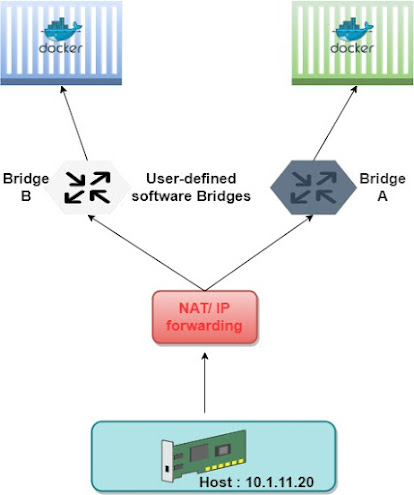
Bridge-based networking:
A bridge is a device (software or hardware) that forwards traffic between different networks.
Containers that are connected to the same bridge device can communicate with each other.
Containers that are connected to different bridge devices are isolated from each other.
Important:
Bridges apply to containers running on the same host.
Remark:
Containers by default connect to the default bridge.
Examples:
Default bridge:
We use the below command to publish an internal container port and its corresponding host port.
User defined bridges can also help isolate container from each other, We can define different bridges and attach different containers to them.
Containers attached to two different bridges can't communicate by default.
Overlay and underlay networks:
If we want different containers on different hosts to communicate with each other, we use the Overlay-networking.
Overlay-networking also provide load-balancing and rerouting in case for example the load-balancer directs us to the another host/container within the swarm overlay cluster of hosts.
Containers in the Overlay network have two IP addresses:
Internal IP: These addresses exist only in the Overlay virtual network for communication between containers.
External IP: is used to transport traffic on the underlay physical network composed of router, switches,....
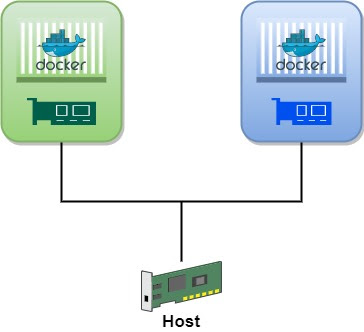
Mcvlan driver:
Briefly, the driver allows the container to have its own MAC address and TCP/IP stack, it also gives a direct access to the containers from the outside without the need for port mapping.
As a result a container with a Macvlan is seen from the outside as "regular" machine in the network.

















Comments