Linux 101 : PAM - Pluggable Authentication Modules -
When we use the PAM (Pluggable Authentication modules), it handles the authentication for us instead of the "login" program.
In case we want to use different authentication plugins, we could stack them up or use them individually, as they could be easily integrated and managed by the PAM system, for example "fingerprint authentication".
We could find the PAM configuration files in the below directories:
- /etc/pam.d
- /etc/pam.d/login
- /etc/pam.d/sshd
The content of the PAM configuration file has the below format:
Below are the different types of modules of a PAM system:
- Auth modules : checks usernames and passwords
- Account name : checks if a user is allowed to access a system, for example account could be configured to be used only on certain days.
- Password : used to change passwords, set expiry date, ...
- Session: handles the user session, such as mounting directories
Modules could be stacked on top of each other, making up layers of authentication and security.
Flags:
Interpret the exit status of the above modules and dictates the action
required:
required:
- Required: success of the module is needed for a successful authentication
- Requisite: works like the required flag, but the user is alerted as soon as the modules fails, and not after all the modules have been tested
- Sufficient: if no "required" module fails the user is successfully authenticated, if is fails it is ignored and the other modules are verified
- Optional: used only when it is the only module available for the authentication device or interface
- Include: used to get configuration from other files
Below are a couple of examples of PAM configuration files:
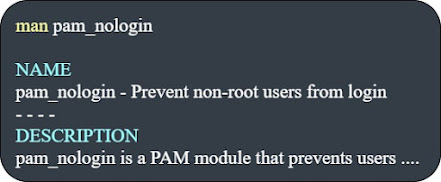
We could find information about each ".so" file - Shared Object - using the "man" command as below:













Comments