Kubernetes 101 : Controlling the cluster - Admission controllers and Webhooks -
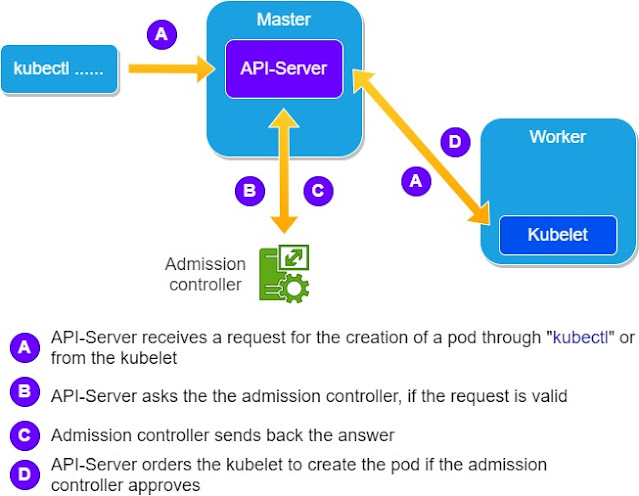
Admission controllers:
For example an admission controller could prevent the creation of pods that don't have a limit on their memory or CPU consumption for example.
The admission controllers monitor the requests going to the API server, then they fulfill or reject them, depending on whether or not the requests adhere to the rules of the kubernetes cluster.
Usually when the request is rejected the client application is informed.
Some admission controllers might change a request to fit certain requirements before validating it.
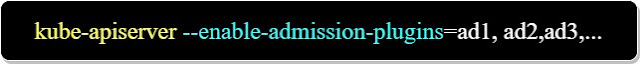
The default admission controllers are enabled by default. We could also, by passing certain parameters to the API server, to enable or disable them.
To enable them for example we could use the below command:
Remark:
You might have to install the "kube-apiserver" utility, if it is not already installed on the machine.
Webhooks:
If for example, a "custom-made" policy is applied on a kubernetes cluster, the default admission controllers can't check them. To check these "custom-made" policies, we use webhooks.
A Webhook is a "personalized" web server usually written in "Go", that are reached through a specific URL.
They process and answer requests coming from the API server.
We have two types of webhooks. The Webhooks that modify a request and send the modified response, and the webhooks that only check he request and return and answer.
We have two types of webhooks. The Webhooks that modify a request and send the modified response, and the webhooks that only check he request and return and answer.












Comments